Event Summary July 6, 2016
2016 Israeli Cyber Security Showcase
Chicago, IL
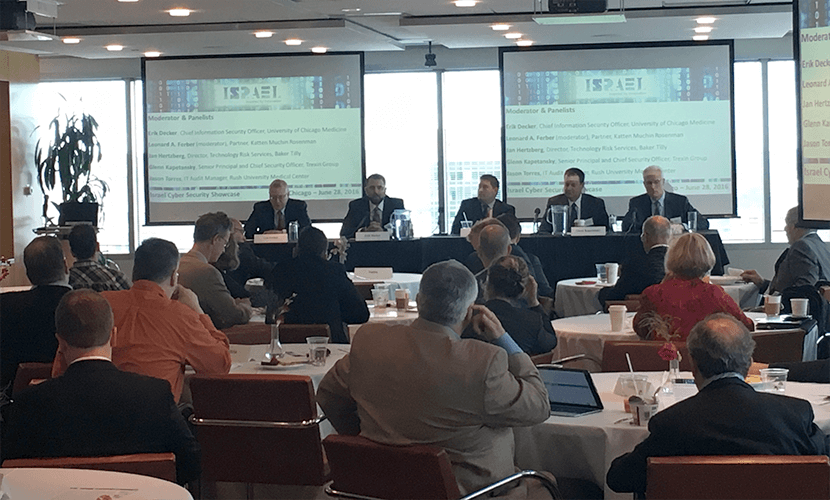
In the spacious downtown Chicago offices of Katten Muchin Rosenman and hosted by the American Israeli Chamber of Commerce, ten Israeli cyber security companies joined a generous crowd of business leaders on the morning of June 28th to hear a rousing panel discussion from the following senior security professionals:
- Erik Decker – Chief Information Security Officer, University of Chicago Medicine
- Jason Torres – IT Audit Manager, Rush University Medical Center
- Glenn Kapetansky – Chief Security Officer, Trexin Group
- Jan Hertzberg – Director of Technology Risk Services, Baker Tilly)
- Len Ferber (moderator) – Partner and co-head of Katten’s Technology Practice.

The discussion explored timely topics and insights into cyber security challenges and directions:
What cyber threats keep us up at night?
- The latest concerns range from tactical (e.g., ransomware) to strategic (how do we detect what didn’t occur, but should have?)
Over the past 12-18 months, what changes have you seen in the types or nature of the cyber security threats you (or your clients) are facing, and how do you (or should your clients) manage the challenge of a changing threat landscape?
- Healthcare threats are increasing vs finance since controls aren’t as mature and personal health information is worth much more on the black market than credit card numbers.
- Ransomware has grown in popularity.
How should companies go about prioritizing the security risks so that you can determine your strategy or road map for dealing with cyber security threats?
- There are a number of good compliance frameworks (Cobit, ISO27000, NIST, 20 CSC, HITRUST, etc.); which is right for your company’s business, your company’s culture, and your customers’ expectations?
- The Board needs to decide their comfort level for risk and funding); the CISO’s job is to communicate the options in business terms the Board can understand, comparable to the other enterprise risks they manage.
Are there best practices that companies should adopt in order to promote more effective communications and understanding within an organization when it comes to cyber security?
- A recent trend is to not only express the cyber security in terms of compliance, metrics, and dashboards, but also in terms of the organizational maturity. That is, don’t just give yourself a check mark, give yourself a 1-5 rating according to the Capability Maturity Model.
How do regulatory mandates impact cyber security decision making within your organization? For example, within the healthcare industry, does HIPAA make decision-making more difficult because you have regulatory framework on top of organizational concerns or easier because it points the way towards what you need to do?
- A good rule of thumb Glenn heard from Arlan McMillan (United Airlines CISO): Compliance is not the same as being secure. But If you are not compliant, you certainly are not secure!
What advice can you give to other companies on how to manage the challenge of vetting different cyber security solutions?
- Look for enterprise-wide risk management based on industry-standard compliance frameworks, not just spot solutions that are “better than the standard.”
- Exciting new areas: Big Data analytics, pattern detection, anti-pattern recognition (i.e., what didn’t happen that should have?), visualization as a detection mechanism.
We got everyone in the room thinking!